Our Services
The following is a list of services we offer through our Consulting and Custom App Dev divisions:
The following is a list of services we offer through our Consulting and Custom App Dev divisions:
Artificial intelligence (AI) is rapidly becoming a crucial technology for developers and businesses to stay competitive in the current digital age. With AI, developers can automate mundane and repetitive tasks, freeing up time to focus on more complex and creative problem-solving. Additionally, businesses can use AI to analyze large amounts of data, gain insights into customer behavior, and make more informed decisions. The benefits of AI extend beyond efficiency and productivity, as it also enables businesses to create more personalized experiences for their customers. In order to succeed in the future, it is essential for developers and businesses to embrace the transformative power of AI and integrate it into their operations.

For 30 years, CODE Consulting has been a leading provider of Custom Application Development services, encompassing AI, cloud, mobile, web, and windows development. Their expertise in these cutting-edge technologies enables them to deliver tailored solutions that leverage artificial intelligence, utilize cloud infrastructure, cater to mobile platforms, create responsive web applications, and build robust Windows applications. With a strong commitment to innovation and a track record of excellence, CODE Consulting empowers businesses to thrive in the digital age.
Are you wondering how AI can help your business? Do you worry about privacy or regulatory issues stopping you from using AI to its fullest? We have the answers!
Our Executive Briefings provide guidance and concrete advice that help decision makers move forward in this rapidly changing Age of Artificial Intelligence and Copilots!
What You Can Expect from Our Expert Team at the Briefing:
Explore the new Age of Artificial Intelligence with confidence and make informed decisions that propel your business forward.
In today's fast-paced and highly competitive business landscape, adopting low-code/no-code scenarios has become crucial for modern organizations striving to stay ahead. This innovative approach empowers non-technical professionals to actively participate in application development and automation processes, eliminating the traditional reliance on scarce IT resources. By enabling citizen developers to create and modify software applications with minimal coding knowledge, low-code/no-code platforms drastically reduce development time and costs, fostering greater efficiency and agility. Moreover, these scenarios promote cross-functional collaboration, allowing diverse teams to collaborate seamlessly and quickly respond to evolving market demands. Embracing low-code/no-code strategies not only accelerates innovation but also enhances organizations' ability to deliver tailored solutions and adapt to changing business requirements, ultimately driving growth and success in the digital era.
Stop managing technical debt and start driving innovation. Legacy software isn't just old code; it’s a bottleneck for growth, a security risk, and a drain on your best talent. For over 25 years, CODE has served as the bridge between aging infrastructure and modern scalability. Whether your goal is cloud migration, mobile accessibility, or a complete architectural overhaul, we provide the proven roadmap to modernize your core business systems without disrupting your current operations.

CODE Security experts are experienced in identifying security vulnerabilities in your products, your services and/or your application's architecture. We are committed to our mission of making your company and its applications more resilient against future attacks and threats.
We have assembled a hand-selected team of senior consultants that bring more than a decade of experience to the table. CODE Security consultants can identify critical vulnerabilities in complex applications and application architectures.

Is your project in trouble? We can help! CODE Consulting brings projects back from the brink of failure. With deep a knowledge process and business to go along with technical knowledge, we are skilled at finding problems and bottlenecks and implementing solutions to get your project back on track. We can't do magic, but most troubled projects are not beyond help. It is usually well worth to spend the time in a short meeting and perform a few hours worth of analysis, for a shot of getting your project back on track.

Visual FoxPro once defined the standard for data-centric application development. Today, while those systems remain functional, they have become “innovation anchors” that limit your ability to scale, secure, and integrate with modern cloud and AI ecosystems. CODE Consulting provides the world’s most specialized path out of VFP. Leveraging over 30 years of FoxPro expertise and our proprietary PJX Analyzer technology, we don't just rewrite your code—we preserve your unique business logic while transitioning you to a high-performance, future-proof .NET environment.

We live in an age of extreme change. This is especially true for software projects. How do you keep up with this and make sure your organization is well positioned to compete tomorrow, next month, and for years to come?
The answer is an investment in your software future that includes experimental projects!
However, running bleeding-edge projects poses many challenges. Does your team have the right skills? Does it have a culture of operating experimental projects that nevertheless result in quick concrete results that can be moved into production? Or is it more likely that a team inexperienced in such projects will fail not because the technology or approach in question failed, but the team simply was ill-equipped to succeed in such a setup?
We can help you set up and run successful “skunk works” projects, similar to the ones we have done for our own organization as well as our clients! Skunk Works projects can be small pilot projects that run for a few days or weeks, or they can be entire teams of people (potentially including yours and ours together) that operate continuously.
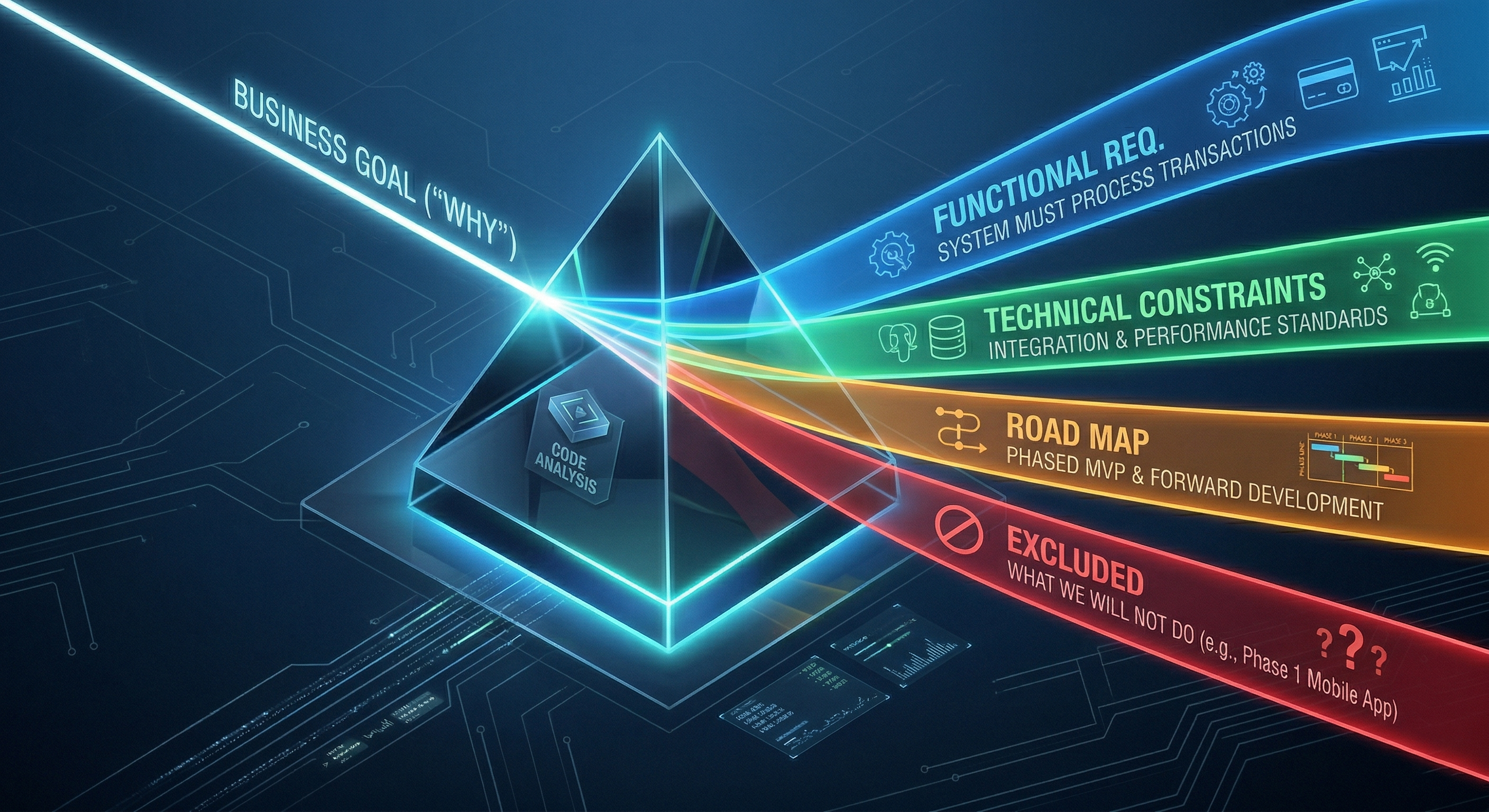
Build your software on a foundation of certainty, not assumptions. The Vision and Scope Workshop is our signature strategic engagement designed to align stakeholders, identify technical roadblocks, and eliminate the risks that cause 70% of software projects to fail. Whether you are launching a greenfield application or modernizing a legacy system, we provide the architectural blueprint and feasibility roadmap you need to move forward with total confidence.

Your web application is the primary touchpoint for your customers and the engine of your internal operations. In an era where users expect sub-second responsiveness and cross-device ubiquity, “just having a website” isn't enough. CODE Consulting specializes in building high-performance, secure, and scalable web applications that solve complex business problems. From enterprise-grade internal tools to high-traffic customer portals, we deliver modern web solutions that drive ROI and eliminate technical debt.
Maximize productivity with high-performance Windows applications built for the modern enterprise. While web and mobile platforms have their place, the Windows desktop remains the de-facto standard for power users who require deep hardware integration, complex data processing, and sub-second responsiveness. CODE Consulting specializes in architecting and delivering rich Windows business applications that are secure, scalable, and fully integrated into your existing ecosystem.